Managing Ssh Git Keys
Like many developers, I would guess, I have many ssh keys. Keys for various services such as github, bitbucket, and others, each with the potential for multiple accounts. Managing these keys when using git on the command line can be a pain, but I’ve got a decent working solution.
ssh-agent
ssh-agent is a process that sits around and helps ssh do its thing on your behalf. There are several helper apps which allow you to configure its behavior, but specifically we are interested in ssh-add.
ssh-add is your friend, especially on Mac OS X.
It can be used to store credentials which, upon a connection attempt, ssh will use. ssh will try all the credentials in the list until it finds one which works.
You can get a listing of what keys are already “known” by the agent with ssh-add -l:
1 2 3 4 5 | |
And here’s the awesome-sauce… you can add keys whose credentials get stored in the keychain with ssh-add -K <path_to_private_key>:
1 2 3 4 5 | |
So, if your ssh key has a passphrase on it, that passphrase is now stored in your Mac OS X keychain, and when ssh is looking for credentials to make the connection with it can find the key and use it without you needing to enter your passphrase again.
Win.
HTTPS
Further, for bonus points, when you’re not using ssh, but rather https, you can still use the keychain…
Being on Mac OS X, we have the osxkeychain which can be used to store and retrive the kind of information we need for authentication.
To set this up, add (or ensure it is already there) the helper line in the [credential] section of your ~/.gitconfig file:
1 2 3 | |
This will allow git to query the OS keychain when it is looking for stored credentials.
If you have multiple accounts on the same system, you may want to tie a set of credentials to the full repository path, so you can access different repositories with different credentials. That’s what the useHttpPath = true line does.
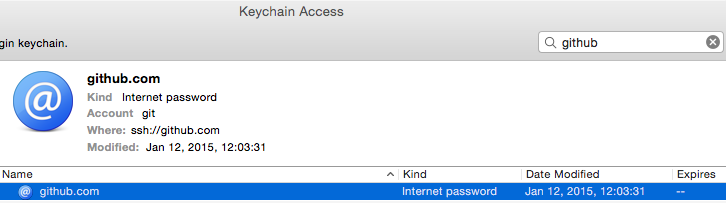
Now, once you authorize a connection to a specific repository those credentials will be stored in your keychain:
Win a second time.